The sudden collapse of the centralized C2K educational network in Northern Ireland has sent shockwaves through the region’s academic sector, forcing a total digital blackout for hundreds of thousands of users. This massive disruption reached into every corner of the provincial school system, effectively severing the connection between approximately 300,000 students and 20,000 educators who rely on the platform for daily instruction and resource management. Upon detecting the intrusion, technical teams were forced to initiate an immediate and total termination of all online services to prevent the potential spread of malicious code throughout the infrastructure. This incident serves as a stark illustration of the inherent risks associated with modern, highly centralized learning networks, where a single point of failure can instantaneously paralyze educational delivery for an entire geographic territory. While the immediate focus shifted toward containment, the long-term implications for digital governance have become a primary concern for local officials.
Response Strategies: Managing Internal System Security
In the immediate aftermath of the breach, the Education Authority worked alongside technical specialists from Capita and external forensic experts to execute a rigorous containment protocol. This strategy prioritized the isolation of affected segments of the network, accompanied by a mandatory region-wide password reset for all users to reclaim administrative control over the digital environment. Despite the widespread nature of the outage, preliminary forensic audits suggested that sensitive student data remained uncompromised, as no evidence of data exfiltration or corruption was discovered during the initial sweep. The decision to maintain a total lockdown of the system reflected a cautious approach that favored long-term security over short-term accessibility, ensuring that the recovery process would not introduce new vulnerabilities into the already fragile ecosystem. Technicians focused on scrubbing the environment and verifying the integrity of every access point before restoration.
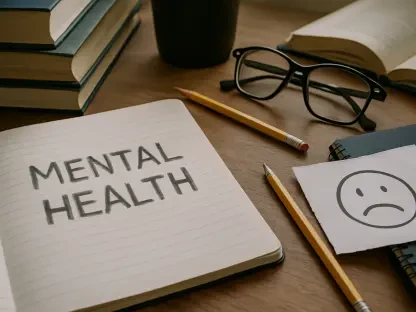
The timing of the cyberattack proved particularly problematic for students preparing for high-stakes GCSE and A-level examinations, as the loss of digital materials threatened to derail their study schedules. To address this crisis, several secondary schools took the extraordinary step of opening their doors during the traditional Easter holiday break, providing in-person teaching support and access to physical textbooks for those who could no longer reach their online portfolios. This shift back to analog methods highlighted the vulnerability of a curriculum that has become increasingly dependent on cloud-based availability for essential revision tools and coursework submissions. While the physical classrooms provided a temporary refuge, the lack of digital access underscored a growing digital divide between students who had offline resources and those who relied entirely on the C2K portal. Administrators recognized that maintaining continuity in a crisis required a hybrid approach that blended technological resilience with flexible logistical planning.
Future Resilience: Strengthening Educational Infrastructure
Educational institutions have become increasingly attractive targets for sophisticated cybercriminals who view the vast amounts of personal data and the critical nature of academic schedules as high-leverage assets. This incident in Northern Ireland mirrors a broader global trend where primary and secondary education systems face relentless pressure from external threats seeking to exploit gaps in legacy software or underfunded security departments. The consensus among cybersecurity professionals is that the rapid digital transformation of schools must be matched by an equally robust investment in defensive infrastructure and real-time monitoring capabilities. Relying on a single centralized system offers administrative efficiency, but it also creates a monolithic target that, if successfully breached, leaves no redundancy for the users who depend on it daily. Developing more decentralized or modular architectures might provide a necessary safeguard, allowing portions of the network to remain functional while others undergo isolation and repair during an active threat cycle.
The resolution of the crisis necessitated a significant shift in how regional authorities prioritized their technological investments and incident response planning for the coming years. Officials realized that static security measures were no longer sufficient and moved toward implementing automated threat detection systems that could identify anomalies before they escalated into full-scale outages. This experience highlighted the urgent need for comprehensive training programs that educated both staff and students on the fundamentals of digital hygiene and the identification of phishing attempts. By transitioning to a more resilient framework, the educational system aimed to ensure that academic continuity remained protected against increasingly complex digital intrusions. The focus shifted toward creating a culture of proactive defense, where every participant in the network understood their role in maintaining the integrity of the collective environment. Ultimately, the lessons learned from this disruption paved the way for a more robust and secure educational future that successfully balanced innovation with safety.